New LPE Security Vulnerability Discovered in Linux Kernel
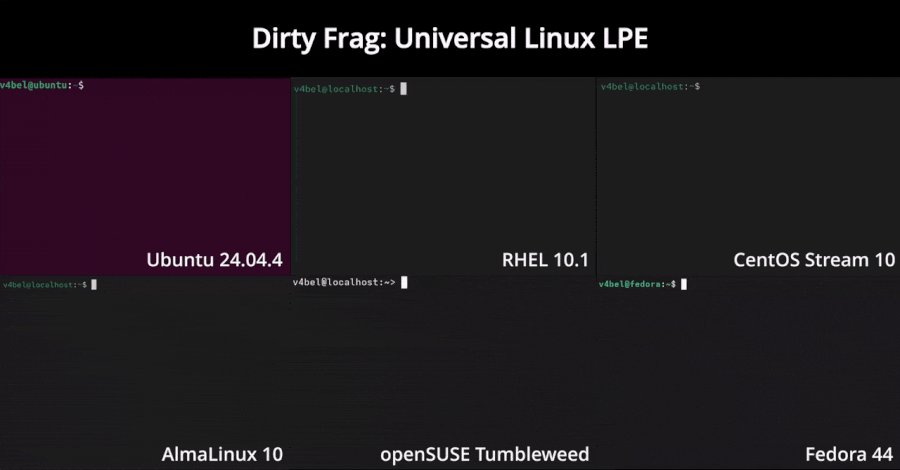
A new, unpatched Local Privilege Escalation (LPE) exploit named Dirty Frag has been discovered in the Linux kernel. This vulnerability allows attackers to gain root access to systems running various Linux distributions. Dirty Frag is considered a successor to the recently discovered LPE vulnerability Copy Fail (CVE-2026-31431), which is already being actively exploited. The vulnerability has been reported to the maintainers of the Linux kernel, but no patch has been released yet. The discovery of Dirty Frag comes at a time when the security of Linux-based systems is increasingly under pressure.
The vulnerability could potentially be exploited in a variety of environments, raising the urgency for a solution. The security assessment of Dirty Frag has not yet been officially determined, but it is expected to receive a high CVSS score, similar to Copy Fail, which was rated at 7.8. This rating indicates a significant risk that administrators and security teams should take seriously. The Copy Fail vulnerability was recently discovered and has already led to a wave of attacks. Security researchers warn that Dirty Frag could be exploited in the same manner, underscoring the need for immediate measures to secure systems.
The exact technical workings of Dirty Frag are not yet fully documented. The Linux community has responded to the discovery by urging users to monitor their systems and regularly install security updates. The proliferation of exploits targeting these vulnerabilities could jeopardize the integrity of servers and end-user systems. Some distributions have already announced that they are working on a patch to mitigate the impact of Dirty Frag. However, the exact timeline for the release of these updates remains unclear.
Administrators are advised to regularly check their systems and ensure that all security policies are adhered to. The discovery of Dirty Frag is further evidence of the ongoing challenges in cybersecurity, particularly in the open-source domain. The need to quickly identify and address vulnerabilities is becoming increasingly urgent as attackers develop more sophisticated methods to exploit weaknesses. The Linux community has previously demonstrated its ability to respond swiftly to security threats.
Collaboration between developers, security researchers, and users is crucial to minimize the impact of such vulnerabilities. The next steps will be critical to ensuring the security of the affected systems. The Dirty Frag vulnerability was disclosed on May 10, 2026, and the community is already working on solutions to mitigate the risks.









💬 Comentarii (0)
Inca nu exista comentarii. Fii primul!