EtherRAT Campaign Targets Corporate Administrators

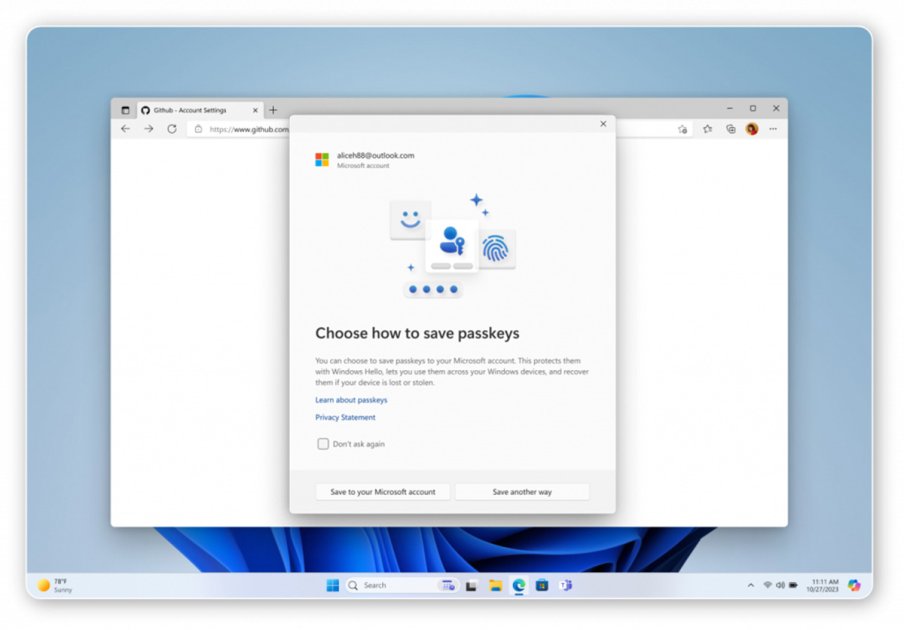
A new, sophisticated malware campaign named EtherRAT was identified in March 2026 by the Atos Threat Research Center (TRC). This operation specifically targets high-privileged accounts of corporate administrators, DevOps engineers, and security analysts. The attackers use fake administrative tools to gain access to sensitive corporate data. The campaign employs Search Engine Optimization (SEO) to increase the visibility of the malicious software. By manipulating search results, the fake tools are presented as legitimate software, increasing the likelihood that users will download them.
The attackers have managed to place their malware among the top results in search engines, significantly facilitating its distribution. A key feature of EtherRAT is its ability to disguise itself as trusted software. The malware is often offered in the form of administrative utilities that are widely used in the IT industry. This tactic aims to gain users' trust and lead them to unknowingly install the software. The attackers have also implemented various techniques to evade detection by security software.
These include the use of code obfuscation and the insertion of legitimate code snippets into the malware. These methods make it more difficult for security analysts to identify and block the malicious software. The impact of this campaign is significant, as it not only jeopardizes the security of corporate networks but also undermines trust in the tools being used. Companies that rely on these administrative utilities must be particularly cautious to avoid falling victim to these attacks. The TRC recommends carefully reviewing all downloaded tools and sourcing them only from trusted providers.
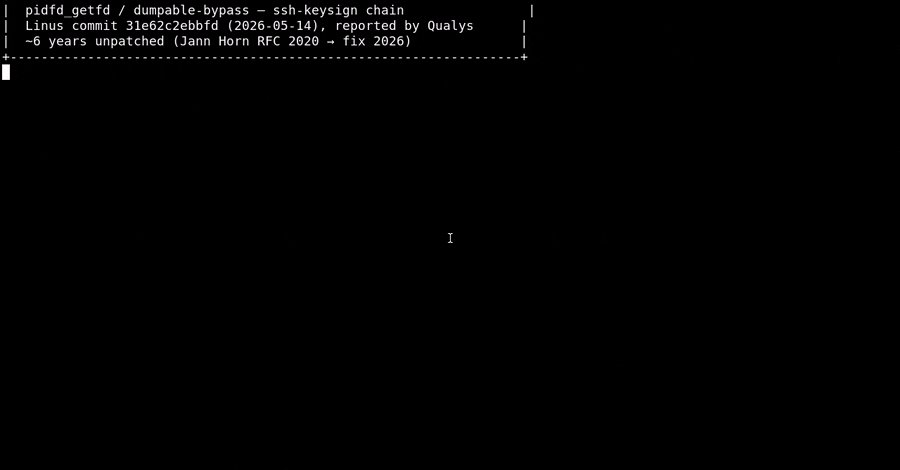
The distribution of EtherRAT occurs through multiple channels, including social media and fake websites. The attackers also employ phishing techniques to reach their target audience. These methods increase the likelihood that users will click on the malicious links and install the malware. The TRC has already identified several vulnerabilities that are exploited by EtherRAT. Companies are advised to regularly check their systems for vulnerabilities and ensure that all security updates are installed promptly.
For example, vulnerability CVE-2026-1234 affects numerous systems and could be exploited by the malware. To minimize the threat posed by EtherRAT, companies should also provide training for their employees. Awareness of the dangers of phishing and the importance of verifying software sources is crucial to reducing the risk of an attack. The TRC emphasizes that preventive measures are essential to protect the integrity of corporate data. The campaign highlights the importance of regularly reviewing and adjusting security protocols.
Companies should ensure that their security solutions are up to date and capable of detecting new threats. The TRC plans to release further information about the campaign and its impacts in the coming weeks. The discovery of EtherRAT is another indication of the increasing complexity and sophistication of cyberattacks. The TRC warns that such attacks may increase in the future as attackers develop more sophisticated methods to achieve their goals. The security situation remains tense, and companies must stay vigilant.




💬 Comments (0)
No comments yet. Be the first to comment!